Blogs about Best Practices
Strengthening Software Security Under the EU Cyber Resilience Act: A High-Level Guide for Security Leaders and CISOs
Get guidance on key tenets of the EU CRA and how Legit can help address them.
Read More.png?width=740&height=220&name=Legit-NewAICapabilities-2%20(1).png)

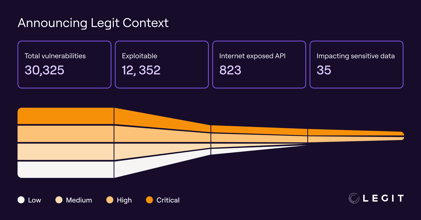
How Legit Is Using Classic Economic Tools to Prevent Application Vulnerabilities
Prevent vulnerabilities and learn how Legit uses data-driven methods like the Lorenz Curve and the Gini Index to uncover high-risk areas in your SDLC.
Read More.png?width=740&height=220&name=ASPM_1200x627%20(2).png)

The Power of Identifying Continuously Vulnerable Repositories (CVRs)
Legit Security is redefining application security by analyzing CVRs, helping enterprises prevent vulnerabilities from recurring in their SDLC.
Read More


How to Reduce Risk From Exposed Secrets
Understand how secrets end up exposed, and how to prevent this risk.
Read More
Unlocking the Power and Potential of GenAI in Software Development
GenAI's rapid adoption brings with it significant challenges in security, governance, and visibility.
Read More
How to Reduce Risk From Developer Permissions Sprawl
How to Reduce Risk From Developer Permissions Sprawl. Get steps to prevent risky permissions sprawl in your SDLC.
Read More
How to Reduce Risk From Misconfigured Build Assets
How to Reduce Risk From Misconfigured Build Assets. Get steps to prevent risky misconfigurations in your SDLC.
Read More
Software Security Best Practices: Where to Focus First
Software Security Best Practices: Where to Focus First. Get our recommendations on where to focus your software security efforts.
Read More
How to Mitigate the Risk of GitHub Actions
How to Mitigate the Risk of GitHub Actions. Get highlights of our research into the security of GitHub Actions, and our advice on mitigating the risk.
Read More
The Risks Lurking in Publicly Exposed GenAI Development Services
The Risks Lurking in Publicly Exposed GenAI Development Services. Get our research team's analysis of the security of GenAI development services.
Read More
ESG Survey Report Finds AI, Secrets, and Misconfigurations Plague AppSec Teams
ESG Survey Report Finds AI, Secrets, and Misconfigurations Plague AppSec Teams. Find out how your peers are managing application security challenges.
Read More
Preview of State of GitHub Actions Security Report: Security of GH Workflows Building Blocks
Security of the Building Blocks of GitHub Actions Workflows. Understand the security status of GitHub Actions workflows and how to mitigate the risk.
Read More
Why Legit Security Immediately Joined the New Coalition for Secure Artificial Intelligence (CoSAI)
Why Legit Security Immediately Joined Google’s New Coalition for Secure Artificial Intelligence (CoSAI). Get details on CoSAI and why Legit chose to be a part of this forum.
Read More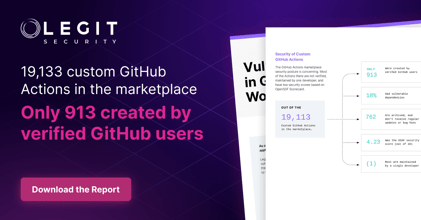
Security of Custom GitHub Actions
Security of Custom GitHub Actions. Get details on Legit's research on the security of custom GitHub Actions.
Read More
Announcing The State of GitHub Actions Security Report
Announcing the State of GitHub Actions Security Report. Get details on Legit's research on the security of GitHub Actions.
Read More
EU Cyber Resilience Act: Updates and Important Requirements
Ensure compliance with the EU Cyber Resilience Act. Learn CRA essentials, how to secure digital products, and how Legit Security helps automate compliance and risk management.
Read More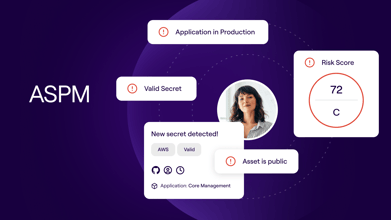
What is ASPM? Application Security Posture Management 101
Learn how Legit Security enhances Application Security Posture Management (ASPM) by automating key processes to ensure business protection.
Read More.png?width=740&height=220&name=Blog%20-%201200%20x%20627%20(2).png)
Security Challenges Introduced by Modern Software Development
Security Challenges Introduced by Modern Software Development. Understand how modern software development is changing security threats.
Read More
Don’t Protect Your Software Supply Chain, Defend the Entire Software Factory
Don't Protect Your Software Supply Chain, Defend the Entire Software Factory. Find out why a too-narrow definition of "supply chain" may be hindering software security efforts.
Read More
Securing the Gateway: Why Protecting Build Systems Is Crucial in Modern Software Development
Securing the Gateway: Why Protecting Build Systems Is Crucial in Modern Software Development. Understand why securing build systems is as important as securing production systems.
Read More
New Survey Finds a Paradox of Confidence in Software Supply Chain Security
New Survey Finds a Paradox of Confidence in Software Supply Chain Security. Get results of and analysis on ESG's new survey on supply chain security.
Read More
Verizon 2024 DBIR: Key Takeaways
Verizon 2024 DBIR Key Takeaways. Get key data points and takeaways from the 2024 Verizon Data Breach Investigations Report.
Read More.png?width=740&height=220&name=Blog%20-%201200%20x%20627%20-%20Ofek%20Haviv%20(V2.1).png)
Dependency Confusion Vulnerability Found in an Archived Apache Project
Dependency Confusion Vulnerability Found in an Archived Apache Project. Get details on the Legit research team's discovery of a dependency confusion vulnerability in an archived Apache project.
Read More
How to Reduce the Risk of Using External AI Models in Your SDLC
How to Reduce the Risk of Using External AI Models in Your SDLC. Understand how AI models add risk and how to address it.
Read More
Securing the Software Supply Chain: Risk Management Tips
Securing the Software Supply Chain: Risk Management Tips. Securing the software supply chain can seem daunting, but with the right strategy, you can optimize your software supply chain risk management practices.
Read More
How to Get the Most From Your Secrets Scanning
How to Get the Most From Your Secrets Scanning. Secret scanning is essential for unlocking next-level software supply chain security. Get tips & best practices for optimal secret scanning to secure your code.
Read More
Microsoft Under Attack by Russian Cyberattackers
Microsoft Under Attack by Russian Cyberattackers. Understand how these attackers are operating and what their tactics mean for security strategies.
Read More
Don't Miss These Emerging Trends in Cloud Application Security
Don't Miss These Emerging Trends in Cloud Application Security. Get details on trends and best practices in cloud application security.
Read More
Using AI to Reduce False Positives in Secrets Scanners
Using AI to Reduce False Positives in Secrets Scanners. Get an overview of how secrets scanners work, and how Legit is reducing secret-scanning false positives..
Read More
Understanding the White House Report on Secure and Measurable Software
Understanding the White House Report on Secure and Measurable Software. Get details on the report, how to address it, and how Legit can help.
Read More
How to Address CISA Attestation
How to Address CISA Attestation. Get details on the CISA Attestation, how to address it, and how Legit can help.
Read More
What to Look for in a Secrets Scanner
What to Look for in a Secrets Scanner. Find out the key capabilities of secrets scanners and what to consider when searching for a solution.
Read More
It's Time to Automate Your Security Testing w/ DevSecOps Tools
Your security is only as good as your team, so why leave it to chance? Learn how automated DevSecOps tools can radically boost your AppSec.
Read More
A Guide to Securing Secrets in CI/CD Pipelines
Dive into the world of software secrets, learn best practices for secure CI/CD, and safeguard sensitive data in this comprehensive guide.
Read More
6 Cloud Application Security Best Practices You Can't Miss
Discover cloud application security best practices: risks, benefits, and strategies for a secure cloud environment.
Read More
Top Vulnerability Management Best Practices and Tips
Master vulnerability management best practices with our guide. Secure your organization using effective strategies and modern techniques.
Read More
Emerging Risks with Embedded LLM in Applications
Learn how the use of Large Language Models (LLMs) like OpenAI's GPT and Google's Bard can create security risks in your applications.
Read More.png?width=740&height=220&name=SEO%20Blog%20%2328%208%20Tips%20to%20Maximize%20Application%20Security%20Testing%20(1).png)
Application Security Testing: Types and Best Practices
Enhance your application security testing and identify vulnerabilities faster. Learn best practices and improve your applications with Legit Security.
Read More
2023 Predictions for Modern Application Security
This blog analyzes trends in application security and predicts the future direction of enterprise application security programs.
Read More.png?width=740&height=220&name=SEO%20Blog%20%2325%20Best%20Vulnerability%20Management%20Tools%20Used%20by%20Enterprises%20(4).png)
How to Choose the Right Vulnerability Management Tools
Discover core functions, benefits, and tips for selecting the best vulnerability management solutions to boost your cybersecurity efforts.
Read More.png?width=740&height=220&name=Blog%20The%20Business%20Risks%20and%20Costs%20of%20Source%20Code%20Leaks%20and%20Prevention%20Tips%20(2).png)
The Business Risks and Costs of Source Code Leaks and Prevention Tips
Protect your business from the serious consequences of code leaks by taking proactive measures to enhance your cybersecurity posture.
Read More
Modern AppSec Needs Code to Cloud Traceability
We talk about why you need code to cloud traceability to modernize your application security and secure your SDLC and CI/CD processes.
Read More
Top 8 Cloud Application Security Challenges and Issues
Discover top cloud security threats and learn effective techniques to keep your cloud applications secure year-round.
Read More.png?width=740&height=220&name=Blog%20Exposing%20Secrets%20(2).png)
Exposing Secrets Via SDLC Tools: The Artifactory Case
Our team investigated how sensitive information can get exposed via SDLC tools that may be used as part of your development pipeline.
Read More.png?width=740&height=220&name=Blog%20Top%20Open%20Source%20Software%20Supply%20Chain%20Security%20Tips%20%20(4).png)
Top Open Source Supply Chain Security Risks & Tips to Prevent
Learn tips to strengthen software supply chain security and address open source software security risks and best practices.
Read More%20-%20Options-1.png?width=740&height=220&name=What%20is%20a%20secure%20SDLC%20(1246%20%C3%97%20700%20px)%20-%20Options-1.png)
What is Secure SDLC? Best Practices for Enhanced Security
Understand SDLC security with our breakdown of each Software Development Life Cycle stage for enhanced software protection.
Read More.png?width=740&height=220&name=GUAC%20(9).png)
GUAC Explained in 5 Minutes
We cover GUAC and its value for your team once GUAC reaches maturity and untangle the complexity of security and dependency metadata.
Read More%20(2).png?width=740&height=220&name=NIST%20Blog%20Image%20Options%20(1246%20%C3%97%20700%20px)%20(2).png)
What are the Five Elements of the NIST Cybersecurity Framework?
This blog details the five elements of the NIST cybersecurity framework and identifies the critical aspects of protecting any org.
Read More
How to Continuously Detect Vulnerable Jenkins Plugins to Avoid a Software Supply Chain Attack
See how attackers used compromised Jenkins plugins to attack the software supply chain and how to continuously detect vulnerable Jenkins plugins at scale.
Read More
Modern AppSec Requires Extending Beyond SCA and SAST
Examining the evolution of application security and why securing the modern SDLC requires organizations to embrace new approaches to supply chain security.
Read More
Integrating Security into DevOps: A Step-By-Step Guide
If you haven’t already been integrating security into DevOps, now’s the time. Learn about the benefits & use this 4-step guide to secure your DevOps.
Read More
GitHub Codespaces Security Best Practices
GitHub configurations aren't secure out of the box. It's up to you to secure them. This blog discusses GitHub's new Codespaces product and how to secure it.
Read More
Software Supply Chain Risks to Be Aware of
Discover four key supply chain risks every CISO must address as software technology evolves and security becomes crucial.
Read More
Software Artifacts Best Practices to Prevent Getting Hacked
Malicious actors are poisoning your artifacts to compromise your software supply chain. Learn how to protect your software artifacts and secure servers.
Read More
8 Best Practices in Cyber Supply Chain Risk Management to Stay Safe
Discover the four types of threats to business software supply chains and the 8 best practices in risk management to help keep them secure.
Read More
10 Agile Software Development Security Concerns You Need to Know
Agile development methodology has become increasingly popular, but it doesn’t come without security concerns. Get to know the top 10 agile software development security concerns you face.
Read More
How Was LastPass Compromised?? Software Supply Chain Attack Tips
LastPass data breach: unauthorized access compromised developer accounts and proprietary source code. Learn about the LastPass security incident details and how to protect your business.
Read More
How to Secure Your Software Supply Chain in 10 Steps
Create a Secure Software Supply Chain in 10 Easy Steps In today’s age of security breaches, it’s more important than ever to create a secure software supply chain. Follow these 10 easy steps to keep your business safe.
Read More
Secure Software Development Lifecycle (SDLC): Key Phases Guide
Explore how to seamlessly integrate security into SDLC phases, transforming your development process to achieve enhanced protection and resilience.
Read More
Data Security Best Practices to Code Securely and Protect Your Data
Boost your business with secure coding practices. Explore our list to improve data security practices and ensure success in your SDLC.
Read More
Secure GitHub: How to Keep Your Code and Pipelines Safe from Hackers
Is GitHub safe? Discover how developers can avoid misconfigurations and vulnerabilities to ensure secure collaboration on GitHub.
Read More
A 10-Step Application Security Risk Assessment Checklist
An application risk assessment is an essential tool to help security and development teams spot hidden vulnerabilities before they become a problem.
Read More
GitHub Security Best Practices Your Team Should Be Following
This article will explain why security and GitHub should go hand in hand and describes a few best practices we believe any organization using GitHub should employ to reduce GitHub security risks.
Read More%20(1).jpg?width=740&height=220&name=piqsels.com-id-ffffi%20(1)%20(1).jpg)
Forget about DevOps, It’s Time to Adopt the DevSecOps Mindset
Debunk common DevSecOps myths and discover why understanding the actual role of DevSecOps is essential for modern security and development practices.
Read More
What Are Immutable Tags And Can They Protect You From Supply Chain Attacks?
Some tags cannot be trusted to reference the same object all the time, and can be changed without the users’ knowledge, opening the door to a supply chain attack.
Read More
Vulnerable GitHub Actions Workflows Part 2: Actions That Open the Door to CI/CD Pipeline Attacks
We examine a bug we’ve found in a popular third-party GitHub action and how it could lead to your SDLC pipeline being attacked. Read more to improve GitHub security and secure your software supply chain.
Read More
Vulnerable GitHub Actions Workflows Part 1: Privilege Escalation Inside Your CI/CD Pipeline
Learn how Legit Security discovered a vulnerable GitHub actions workflow. Get details on the vulnerability and and what you can do to mitigate it.
Read MoreRequest a Demo
Request a demo including the option to analyze your own software supply chain.