Featured Resources
White paper
AppSec in the Age of AI
Understand the new application security requirements when AI writes code.
Read NowAnalyst Reports
Gartner® Report: Why Vibe Coding Needs to Be Taken Seriously
In this Gartner® report, the authors predict “by 2028, 40% of new enterprise production software will be created with vibe coding techniques and tools.”
Read MoreWhite Paper
Reality Check on Securing AI-Generated Code
We surveyed 117 security pros to understand their priorities, plans, and pains around AI-led software development.
Read NowMore Coding, Less Remediating: How ASPM Boosts Developer Productivity and the Bottom Line
Get details on the business benefits Legit customers realize.
Read Now2025 State of Application Risk
Legit Security’s new 2025 State of Application Risk report gives you a snapshot of where application security risk lives in the modern development environment.
Read MoreAnalyst Reports
Frost Radar™: Global Application Security Posture Management (ASPM) 2024
Dive deeper into the ASPM market and Legit’s place in it in Frost & Sullivan’s Frost Radar™: Global Application Security Posture Management (ASPM) 2024 report.
Read MoreSort
Name Date Content Type
Filters
All Analyst Reports Case Studies Datasheets eBooks Guides Infographics Solution Briefs Videos Webinars White Papers News Press Releases X
-
 Read Nowwhite papers
Read Nowwhite papers2025 State of Application Risk
January 23, 2025
2025-01-23 00:00:00
Legit Security’s new 2025 State of Application Risk report gives you a snapshot of where application security risk lives in the modern development environment.
-
 Read Nowanalyst reports
Read Nowanalyst reportsGartner® Report: Why Vibe Coding Needs to Be Taken Seriously
June 18, 2025
2025-06-18 00:00:00
In this Gartner® report, the authors predict “by 2028, 40% of new enterprise production software will be created with vibe coding techniques and tools.”
-
 Read Nowanalyst reports
Read Nowanalyst reportsGartner® Innovation Insight: Application Security Posture Management
January 21, 2025
2025-01-21 00:00:00
In the Gartner® Innovation Insight: Application Security Posture Management report, the authors note that “By 2027, 80% of organizations in regulated verticals utilizing AppSec testing will incorporate some form of ASPM, in contrast to the current adoption rate of 29%.”
-
 Watch Nowwebinars
Watch NowwebinarsLive Demo: Secrets Detection and Prevention 2.0
January 9, 2025
2025-01-09 00:00:00
See how Legit's secrets scanning solution can help you tackle the entire issue of secrets exposure. Watch the recording now.
-
 Watch Nowwebinars
Watch NowwebinarsThe Top 6 Unknown SDLC Risks Legit Uncovers Webinar
November 21, 2024
2024-11-21 00:00:00
What risks are new Legit customers surprised to find lurking in their SDLCs? Watch the webinar on-demand to find out.
-
 Watch Nowwebinars
Watch NowwebinarsThe Open-Source Trap: How Legacy Secrets Scanners Fail Against Modern Threats
October 24, 2024
2024-10-24 00:00:00
Discover why secrets have become the top initial attack vector for threat actors.
-
 Read Nowanalyst reports
Read Nowanalyst reportsFrost Radar™: Global Application Security Posture Management (ASPM) 2024
October 2, 2024
2024-10-02 00:00:00
Dive deeper into the ASPM market and Legit’s place in it in Frost & Sullivan’s Frost Radar™: Global Application Security Posture Management (ASPM) 2024 report.
-
 Watch Nowwebinars
Watch NowwebinarsGitHub Actions Exposed: Securing Critical Code Automation that Runs Your Software Factory
August 21, 2024
2024-08-21 00:00:00
Learn why GitHub Actions can quickly hand attackers the keys to your company’s most critical code infrastructure — without the right controls and protections in place, the implications are more severe than you may know.
-
 Read Nowanalyst reports
Read Nowanalyst reportsESG Survey Report: Modernizing Application Security to Scale for Cloud-Native Development
August 16, 2024
2024-08-16 00:00:00
Learn why security teams need to keep pace to effectively manage risk and protect applications from threats.
-
.png?width=1600&height=900&name=Webinar%20Card%20-%20SDLC%20with%20ASPM%20(1).png) Watch Nowwebinars
Watch NowwebinarsInnovating in Software Security: How to Take Back Control of Your SDLC with ASPM
July 10, 2024
2024-07-10 00:00:00
Watch this webinar with Joe Nicastro, Legit Security Field CTO, on “Innovating in AppSec: How to Take Back Control of Your SDLC with ASPM,” where we delve into cutting-edge strategies to implement a holistic approach to application security posture management (ASPM).
-
 Read Nowanalyst reports
Read Nowanalyst reportsESG Survey: The Growing Complexity of Securing the Software Supply Chain eBook
April 18, 2024
2024-04-18 00:00:00
TechTarget’s Enterprise Strategy Group recently surveyed 368 IT, cybersecurity, and application development professionals to understand current software development practices, the impact and challenges of software supply chain attacks, and how organizations are using software supply chain security solutions.
-
 Read Nowcase studies
Read Nowcase studiesVulnerability management case study: Cybersecurity vendor
June 30, 2023
2023-06-30 00:00:00
This Cybersecurity vendor has long been one of the most trusted names in cybersecurity, delivering “dynamic cyber defense solutions by combining services and products powered by industry-leading expertise, intelligence and innovative technology.
-
 Read Nowcase studies
Read Nowcase studiesKraft-Heinz | Ricardo Lafosse
September 15, 2023
2023-09-15 00:00:00
Hear how Ricardo Lafosse, CISO at Kraft-Heinz, uses Legit Security's auto-discovery and analysis capabilities to find vulnerabilities and collaborate effectively with development teams to ensure secure application delivery.
-
 Read Nowcase studies
Read Nowcase studiesCompliance case study: ACV Auctions | Erik Bataller
July 2, 2023
2023-07-02 00:00:00
ACV Auctions is out to “fundamentally change the wholesale automotive industry by providing a level of trust and transparency that was once unimaginable.”
-
 Read Nowcase studies
Read Nowcase studiesVulnerability management case study: Firebolt Analytics | Nir Yizhak
July 28, 2023
2023-07-28 00:00:00
Firebolt's mission is “to create the world’s most powerful cloud data warehouse and offer it as a service.” As a company that is “first and foremost customer driven”, earning their customers’ trust is built not only on product innovation but on the confidence that Firebolt will do what it takes to protect their proprietary and sensitive data.
-
 Read Nowcase studies
Read Nowcase studiesSDLC visibility case study: Noname Security | Karl Mattson
September 22, 2023
2023-09-22 00:00:00
Despite the moniker, Noname Security is making a big name for themselves in the world of API security by protecting some of the world’s largest organizations from API-based attacks.
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialCISO | Consumer Goods
May 24, 2024
2024-05-24 00:00:00
"Application Security Posture Management Done Right."
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialCISO | IT Services
May 24, 2024
2024-05-24 00:00:00
"Legit Secures Your Code Pipelines And Identifies Stale And Noncompliant Repositories."
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialCISO | Software
May 24, 2024
2024-05-24 00:00:00
"Legit Security Is The Centerpiece Of Our Product Security Program."
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialInfoSec | Banking
July 2, 2023
2023-07-02 00:00:00
"Great Tool and An Even Better Team."
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialDirector | Banking
May 24, 2024
2024-05-24 00:00:00
"Legit's Remarkable Responsiveness And Dedication To Success."
-
 Read Nowcustomer testimonial
Read Nowcustomer testimonialInfoSec | Consumer Goods
July 2, 2023
2023-07-02 00:00:00
"How Legit Team Exceeds In Delivering Commitments and Customer Assistance."
-
 Read Nowsolution briefs
Read Nowsolution briefsLegit Secret Scanning Solution Brief
January 22, 2024
2024-01-22 00:00:00
Learn how Legit Secret Scanning helps meet the unique challenge of managing secrets in the SDLC.
-
 Read Nowsolution briefs
Read Nowsolution briefsLegit Security Solution Brief
April 1, 2023
2023-04-01 00:00:00
The Legit Security platform secures your software supply chain environment with automated discovery, security policies, risk remediation, risk scoring, and compliance.
-
 Read Nowdatasheets
Read NowdatasheetsLegit-Crowdstrike Joint Solution Brief
August 23, 2023
2023-08-23 00:00:00
Learn how Crowdstrike and Legit Security help security and development teams scale up security from code to cloud in this joint-solution brief.
-
 Read Nowdatasheets
Read NowdatasheetsLegit-Snyk Joint Solution Brief
June 23, 2023
2023-06-23 00:00:00
Learn how Snyk and Legit Security help security and development teams scale up security from code to cloud in this joint-solution brief.
-
 Read Nowwhite papers
Read Nowwhite papersApplication Security Posture Management (ASPM) From Code To Cloud: The Business And Security Benefits eBook
June 25, 2023
2023-06-25 00:00:00
Securing the SDLC without disrupting the rapid pace of modern CI/CD and DevOps processes is challenging for AppSec teams. Download this eBook to learn how code to cloud ASPM helps organizations overcome these problems and delivers immediate, tangible benefits for secure software delivery.
-
 Read Nowinfographics
Read NowinfographicsWhy You Need ASPM Now
October 1, 2023
2023-10-01 00:00:00
Download the Why You Need ASPM Now infographic on why you need automated compliance reporting and real-time visibility with Legit Security's ASPM platform.
-
 Read Nowinfographics
Read NowinfographicsHow ASPM Saves Organizations Money
October 1, 2023
2023-10-01 00:00:00
Download the How ASPM Saves Organizations Money and how Legit's Application Security Posture Management (ASPM) platform drives efficiency.
-
 Read Nowinfographics
Read NowinfographicsOvercoming the Compliance Challenges of AppSec
November 22, 2023
2023-11-22 00:00:00
Download the Overcoming the Compliance Challenges of AppSec why you need automated compliance reporting and real-time visibility with Legit Security's ASPM platform
-
 Read Nowdatasheets
Read NowdatasheetsAddressing CISA Attestation
March 1, 2024
2024-03-01 00:00:00
Understand CISA Attestation requirements and how Legit can help.
-
 Read Nowdatasheets
Read NowdatasheetsComplying with NIST SSDF
March 25, 2024
2024-03-25 00:00:00
The National Institute of Standards and Technology (NIST) Secure Software DevelopmentFramework (SSDF) is “a set of fundamental, sound practices for secure software development.”NIST created the SSDF standard as a result of the President’s 2021 Executive Order (EO) on“Improving the Nation’s Cybersecurity.”SSDF requirements are now mandatory for companies that want to sell their software to thegovernment.
-
 Read Nowdatasheets
Read NowdatasheetsSecrets Use Case
September 1, 2023
2023-09-01 00:00:00
Legit Security automatically scans the SDLC for secrets, delivering code to cloud traceability that lets organizations quickly identify their origin, propagation, criticality, and the exact code where they are being used.
-
 Read Nowdatasheets
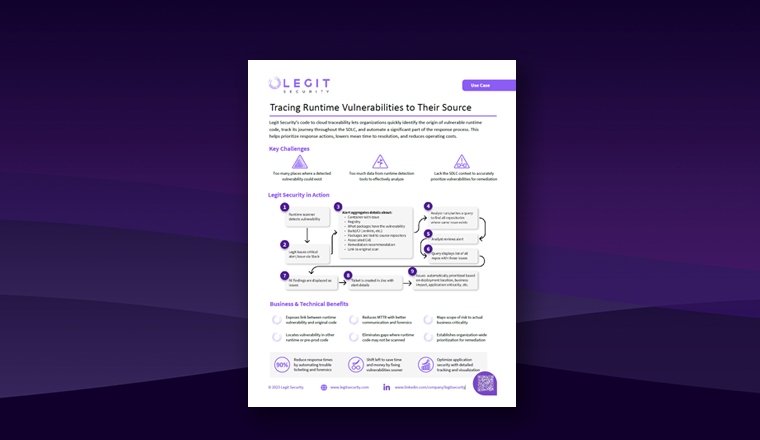
Read NowdatasheetsVulnerabilities in Runtime
August 1, 2023
2023-08-01 00:00:00
Legit Security’s code to cloud traceability lets organizations quickly identify the origin of vulnerable runtime code, track its journey throughout the SDLC, and automate a significant part of the response process.
-
 Watch Nowvideos
Watch NowvideosBackstage at RSA '22 | Interview with Roni Fuchs at RSA 2022
August 31, 2022
2022-08-31 00:00:00
Watch Roni Fuchs, Co-founder and CEO of Legit Security, give a backstage interview at the Legit Security booth at RSA 2022, located in San Francisco's Moscone Center.
-
 Watch Nowvideos
Watch NowvideosConnect Without Fear
May 20, 2024
2024-05-20 00:00:00
Watch “Connect Without Fear” to understand how we’re helping enterprises know their application security posture is legit – and prove it.
-
 Watch Nowvideos
Watch NowvideosHow Legit Helps Teams Proactively Protect -- and Prove It
May 20, 2024
2024-05-20 00:00:00
Watch “How Legit Helps Teams Proactively Protect -- and Prove It” to better understand how we are helping enterprises.
-
 Watch Nowvideos
Watch NowvideosLegit Security Interview with Roni Fuchs at RSA 2023 | Backstage at RSA '23
June 19, 2023
2023-06-19 00:00:00
Watch Roni Fuchs, Co-founder and CEO of Legit Security, give a backstage interview at the Legit Security booth at RSA 2023, located in San Francisco's Moscone Center.
-
 Watch Nowvideos
Watch NowvideosNYSE TV: Interview with Legit Security CEO, Roni Fuchs
July 17, 2023
2023-07-17 00:00:00
Watch the Roni Fuchs, co-founder and CEO of Legit Security, interview with NYSE, which is also a customer of Legit Security.
-
.png?width=1280&height=720&name=Paychex%20CISO%20Bradley%20Schaufenbuel%20Interviews%20Legit%20CEO%20Roni%20Fuchs%202024%20-%20YouTube%20Thumbnail%20(1).png) Watch Nowvideos
Watch NowvideosPaychex CISO Bradley Schaufenbuel Interviews Legit CEO Roni Fuchs 2024
May 23, 2024
2024-05-23 00:00:00
Join us for an exclusive interview featuring Paychex CISO Bradley Schaufenbuel and Legit Security CEO Roni Fuchs.
-
 Watch Nowvideos
Watch NowvideosSecret Scanning Demo
January 22, 2024
2024-01-22 00:00:00
Watch the secret scanning and developer data protection overview, demo, and platform walkthrough.
-
 Watch Nowcase studies
Watch Nowcase studiesCustomer Testimonial | Firebolt
June 19, 2023
2023-06-19 00:00:00
Watch Nir Yizhak, CISO at Firebolt, discuss their challenges and solutions for application security, best practices for developer and security team collaboration, and adjusting to a constantly evolving threat landscape. Find out how the Legit Security Platform helps organizations like Firebolt secure applications from code to cloud with automated SDLC discovery/analysis and real-time application security posture management for the integrity, governance, and compliance of every software release.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on modern attacker tactics
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on scaling security
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on exposing hidden risk
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on prioritizing risk
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on the security-dev relationship
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesNetskope on security champions
March 16, 2023
2023-03-16 00:00:00
Watch James Robinson, Deputy CISO and Director at Netskope, discuss why cybercriminals attack “easy” first and the benefits of the Legit Security Platform in this customer testimonial video.
-
 Watch Nowcase studies
Watch Nowcase studiesKraft-Heinz on improving developer collaboration with Legit
December 13, 2022
2022-12-13 00:00:00
Hear from Ricardo Lafosse, Chief Information Security Officer (CISO) at Kraft-Heinz, on how to prevent and prepare for the next big software supply chain attack.
-
 Watch Nowcase studies
Watch Nowcase studiesKraft-Heinz on Legit’s ease of use
December 13, 2022
2022-12-13 00:00:00
Hear from Ricardo Lafosse, Chief Information Security Officer (CISO) at Kraft-Heinz, on how to prevent and prepare for the next big software supply chain attack.
-
 Watch Nowcase studies
Watch Nowcase studiesKraft-Heinz on defending against supply chain attacks with Legit
December 13, 2022
2022-12-13 00:00:00
Hear from Ricardo Lafosse, Chief Information Security Officer (CISO) at Kraft-Heinz, on how to prevent and prepare for the next big software supply chain attack.
-
 Watch Nowcase studies
Watch Nowcase studiesACV Auctions on SDLC visibility with Legit
November 30, 2022
2022-11-30 00:00:00
Watch Erik Bataller, VP of Information Security at ACV Auctions, discuss the capabilities and benefits of the Legit Security Platform in this customer case study video.
-
 Watch Nowcase studies
Watch Nowcase studiesACV Auctions on better decision-making with Legit
November 30, 2022
2022-11-30 00:00:00
Watch Erik Bataller, VP of Information Security at ACV Auctions, discuss the capabilities and benefits of the Legit Security Platform in this customer case study video.
-
 Watch Nowcase studies
Watch Nowcase studiesACV Auctions on reducing manual work with Legit
November 30, 2022
2022-11-30 00:00:00
Watch Erik Bataller, VP of Information Security at ACV Auctions, discuss the capabilities and benefits of the Legit Security Platform in this customer case study video.
-
 Watch Nowwebinars
Watch Nowwebinars3 Software Supply Chain Security Pitfalls and How to Avoid Them | ISMG
March 20, 2023
2023-03-20 00:00:00
Join Liav Caspi (CTO at Legit Security) and John Tierney (Field CTO at Legit Security) as they reveal the 3 most common software supply chain security pitfalls and how to avoid them.
-
 Watch Nowwebinars
Watch Nowwebinars5 Best Practices to Stop Malicious Submissions in Your Development Pipeline
October 18, 2022
2022-10-18 00:00:00
In this webinar, you will learn the latest best practices to prevent malicious source code modification by external and internal threats.
-
 Watch Nowwebinars
Watch NowwebinarsASPM - The New AppSec Revolution
July 18, 2023
2023-07-18 00:00:00
Watch Liav Caspi (Legit Co-founder) and John Tierney (Field CTO) discuss how Application Security Posture Management (ASPM) revolutionized AppSec.
-
 Watch Nowwebinars
Watch NowwebinarsDetecting and Preventing Software Dependency Attacks | SANS
September 1, 2022
2022-09-01 00:00:00
Watch Liav Caspi, Legit Security Co-founder and CTO, dive into the SANS report on detecting and preventing software dependency attacks.
-
 Watch Nowwebinars
Watch NowwebinarsFinding Dangerous Hardcoded Secrets You Didn’t Know Existed in Your SDLC | SANS
January 19, 2023
2023-01-19 00:00:00
Join Liav Caspi and Roy Blit as they discuss practical methods to prevent software supply chain attacks and reduce the damage caused by hardcoded secrets. Learn about new techniques attackers are using, why accurate visibility, beyond just source code, is paramount, and how to scale secret scanning initiatives effectively.
-
 Watch Nowwebinars
Watch NowwebinarsFortune 500 CISO Insights - Our Fast Track to Software Supply Chain Security | ISSA
October 26, 2022
2022-10-26 00:00:00
Join Ricardo Lafosse, CISO of Kraft Heinz, for a conversation on how his team adopted a modern software supply chain security approach that hardened their SDLC, gained quick adoption by the cross-functional teams and accelerated the maturity of their overall application security program.
-
 Watch Nowwebinars
Watch NowwebinarsGetting AppSec Right: Code to Cloud Traceability and Security | SC Media
May 1, 2023
2023-05-01 00:00:00
Join Liav Caspi, Legit Security CTO, and John Tierney, Legit Security Field CTO, as they discuss Code to Cloud traceability and security.
-
 Watch Nowwebinars
Watch NowwebinarsHow to Shift Security Left - Best Practices From a Fortune 500 DevSecOps Leader | Techstrong
July 27, 2022
2022-07-27 00:00:00
Legit Security customer Bob Durfee at Takeda Pharmaceutical says security leaders have a choice: remediate security issues earlier in pre-production or pay more to fix them later.
-
 Watch Nowwebinars
Watch NowwebinarsProtecting CI/CD Pipelines - Growing Threats and the Keys to Securing Them
June 22, 2023
2023-06-22 00:00:00
Learn the best practices for applying CI/CD security across the entire SDLC, how to evaluate and implement security tools that automate the security function, and how to develop a shared responsibility security culture involving all stakeholders.
-
 Watch Nowwebinars
Watch NowwebinarsProtecting the SDLC: Modernizing Secure Software Delivery with ASPM
October 19, 2022
2022-10-19 00:00:00
Watch Liav Caspi, Legit Co-founder, and James Robinson, Deputy CISO and Director at Netskope discuss the urgent need for ASPM for visibility and security.
-
 Watch Nowwebinars
Watch NowwebinarsReframing Application Security For Modern Apps And Tighter Budgets | ISSA
March 29, 2023
2023-03-29 00:00:00
Join Jason Chan, ex-CISO of Netflix, and Legit Security CTO Liav Caspi, as they discuss the reframing of application security budgets.
-
 Watch Nowwebinars
Watch NowwebinarsSecrets Detection: Why Coverage Throughout the SDLC is Critical to Your Security Posture| ISMG
April 9, 2024
2024-04-09 00:00:00
Join Liam McCamley and Joe Nicastro as they discuss how to detect different types of secrets across your entire SDLC, not just in source code.
-
 Watch Nowwebinars
Watch NowwebinarsSoftware Supply Chain Security – Best Practices to Score & Prioritize AppSec Risks | ISSA
July 20, 2022
2022-07-20 00:00:00
Learn practical tips and best practices to efficiently score and prioritize application security risks from Legit Security customer Erik Bataller at ACV Auctions.
-
 Watch Nowwebinars
Watch NowwebinarsThe Hidden Software Supply Chain Risks That Can Ruin Your Year | Techstrong
May 1, 2022
2022-05-01 00:00:00
Discussion with Liav Caspi, Alex Babar, and Cody Brown on some of the most critical software supply chain risks hidden in plain sight that can ruin your year as a security professional.
-
 Watch Nowwebinars
Watch NowwebinarsWhat You Need to Know About Securing Developer Environments Before It’s Too Late | ISC2
October 20, 2022
2022-10-20 00:00:00
Discussion with Liav Caspi, Alex Babar, and James Robinson, Deputy CISO & Director at Netskope, as they discuss techniques you can use to effectively harden your developer environments.
-
 Watch Nowwebinars
Watch NowwebinarsWhy Visibility is Key to AppSec Efficacy | ActualTuch
April 25, 2024
2024-04-25 00:00:00
Join Joe Nicastro and Jenny Hinz as they discuss why visibility is key to AppSec efficacy and secure software delivery.
-
 Watch Nowwebinars
Watch NowwebinarsSoftware Supply Chain Security – Most Common Attack Patterns and Tips to Mitigate | Schellman
May 1, 2022
2022-05-01 00:00:00
Learn more about common software supply chain attack patterns from security experts Liav Caspi and Jacob Ansari with tips to defend against future attacks.
-
 Read Nowwhite papers
Read Nowwhite papersA New Approach to Application Security
May 2, 2024
2024-05-02 00:00:00
Download the whitepaper and see how Legit is the new way to manage your application security posture for security, product and compliance teams.
-
 Read Nowwhite papers
Read Nowwhite papersBest Practices Guide: Defending Your Software Supply Chains
July 1, 2022
2022-07-01 00:00:00
Guide to the 3 most common attack patterns targeting your software supply chain from industry.
-
 Read Nowwhite papers
Read Nowwhite papersCyberEdge 2024 Cyberthreat Defense Report
May 29, 2024
2024-05-29 00:00:00
Get the CyberEdge 2024 Cyberthreat Defense Report which plays a unique role in collecting statistics on IT cyberattacks and data breaches.
-
 Read Nowwhite papers
Read Nowwhite papersOvercoming the Challenge of Protecting Secrets in the SDLC
January 22, 2024
2024-01-22 00:00:00
Learn what secrets are, how they become embedded in code repositories and across your SDLC, and how to address detection and prevention.
-
 Read Nowwhite papers
Read Nowwhite papersProtecting CI/CD Pipelines: Growing Threats and the Keys to Securing Them | SANS
June 1, 2023
2023-06-01 00:00:00
Learn the real-world benefits of enhanced CI/CD security, CI/CD security best practices, a real-world CI/CD security case study, and how to choose the right solution to protect your environment in this SANS whitepaper.
-
 Take Nowwhite papers
Take Nowwhite papersRapid Risk Assessment
August 22, 2022
2022-08-22 00:00:00
Despite the moniker, Noname Security is making a big name for themselves in the world of API security by protecting some of the world’s largest organizations from API-based attacks.
-
 Read Nowwhite papers
Read Nowwhite papersThe 3 Riskiest Software Supply Chain Attack Patterns Common Across Frameworks
May 1, 2022
2022-05-01 00:00:00
Consolidated guide to the 3 most common attack patterns targeting your software supply chain from industry sources MITRE ATT&CK, CNCF, CAPEC, ENISA, and more
-
 Read Nowwhite papers
Read Nowwhite papersTop Software Supply Chain Security Pitfalls and How to Avoid Them
November 22, 2022
2022-11-22 00:00:00
Learn the pitfalls that are preventing you from effectively securing your software supply chains and gain insights that will help your approach.
-
 Read Nowwhite papers
Read Nowwhite papersWhat You Need To Know About The Software Supply Chain Regulatory Landscape And SBOMs
November 22, 2022
2022-11-22 00:00:00
Download this guide to uncover the most important regulatory changes you need to know about US Executive Order 14028, Secure Software Development Framework, and Software Bill of Materials or SBOMs.
-
 Read Nowwhite papers
Read Nowwhite papersThe State of GitHub Actions Security
January 1, 2024
2024-01-01 00:00:00
Discover how Legit Security enhances AI supply chain security with in-depth insights and solutions. Uncover GitHub Actions security risks and solutions.
-
 Read Nowwhite papers
Read Nowwhite papersThe Top 6 Unknown SDLC Risks Legit Uncovers
October 9, 2024
2024-10-09 00:00:00
Get details on the SDLC risks Legit uncovers and how to prevent them.
-
 Read Nowdatasheets
Read NowdatasheetsLegit Platform Overview
November 14, 2024
2024-11-14 00:00:00
Get an overview of the Legit ASPM platform.
-
 Read Nowdatasheets
Read NowdatasheetsLegit ASPM Overview
November 14, 2024
2024-11-14 00:00:00
Get details on Legit's ASPM capabilities.
-
 Read Nowdatasheets
Read NowdatasheetsLegit Secrets Detection & Prevention Overview
November 14, 2024
2024-11-14 00:00:00
Get an overview of Legit's secrets scanning capabilities.
-
 Read Nowdatasheets
Read NowdatasheetsApplication Security Acronyms Cheat Sheet
November 14, 2024
2024-11-14 00:00:00
Get clarity on AppSec acronyms, from SAST to SCA, ASPM, and CNAPP.
-
 Get Reportwhite papers
Get Reportwhite papersSurvey Report: Use and Security of GenAI in Software Development
November 19, 2024
2024-11-19 00:00:00
We asked 400 security professionals and software developers how they are using and securing GenAI code.
-
 Read Nowdatasheets
Read NowdatasheetsLegit ASPM and Secrets Detection & Prevention: A Comparison
November 25, 2024
2024-11-25 00:00:00
What's right for you? Legit ASPM or Legit Secrets Detection & Prevention?
-
 Watch Nowvideos
Watch NowvideosLegit CEO Roni Fuchs talks to theCUBE and NYSE Wired on the floor of the NYSE
December 17, 2024
2024-12-17 00:00:00
SiliconANGLE Media Inc. Co-Founder and Co-CEO John Furrier hosts Roni Fuchs, Co-Founder & CEO at Legit Security, as part of theCUBE + NYSE Wired presentation of Media Week - Cyber & AI Innovators Summit from the New York Stock Exchange.
-
 Watch Nowwebinars
Watch NowwebinarsWebcast: AppSec & Root Cause Remediation
February 5, 2025
2025-02-05 00:00:00
In this webcast, we explore strategies to help you scale remediation and focus on the issues that drive true risk to your business.
-
 Read Nowpress releases
Read Nowpress releasesLegit Security Brings Business Context to AppSec Issues Prioritization and Remediation
February 24, 2025
2025-02-24 00:00:00
Legit is the first ASPM platform to bolster AppSec program maturity by connecting previously disparate data points, enabling organizations to understand and fix issues creating the most business risk
-
 Watch Nowvideos
Watch NowvideosKey Stats From 2025 State of Application Risk Report
March 6, 2025
2025-03-06 00:00:00
Legit co-founder Liav Caspi shares highlights from the Legit 2025 State of Application Risk report
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: From Data Overload to Actionable Context
March 18, 2025
2025-03-18 00:00:00
Context matters. 35 mph sounds fast in a school zone, but no cause for alarm on a highway. The same can be said for AppSec. Watch the on-demand recording now.
-
 Read Nowdatasheets
Read NowdatasheetsLegit Context
March 31, 2025
2025-03-31 00:00:00
Get details on how Legit context is helping teams fix what matters.
-
.png?width=2000&height=1045&name=Blog-Image-LegitRootCauseRemediation%20(1).png) Read Nowdatasheets
Read NowdatasheetsLegit Root Cause Remediation
March 31, 2025
2025-03-31 00:00:00
Find out how Legit is helping teams address multiple issues with one action.
-
 Watch Nowvideos
Watch NowvideosWhat Is ASPM?
March 31, 2025
2025-03-31 00:00:00
Legit Field CTO Joe Nicastro explains what ASPM is, and how it benefits security and development teams.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: Hidden Requirement in the Telecoms Security Act (TSA)
April 16, 2025
2025-04-16 00:00:00
This webinar looks at the TSA, ECR and Code of Practice from a software development lifecycle perspective, including the software supply chain.
-
 Read Nowwhite papers
Read Nowwhite papersMore Coding, Less Remediating: How ASPM Boosts Developer Productivity and the Bottom Line
June 2, 2025
2025-06-02 00:00:00
Get details on the business benefits Legit customers realize.
-
.png?width=2000&height=1045&name=3%20(1).png) Watch Nowwebinars
Watch NowwebinarsWebinar: AI-Native Software Development: Rewriting Application Security
June 10, 2025
2025-06-10 00:00:00
AI has forever changed software development - in this webinar we explore all things impacting application security in the age of AI.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: Making the Business Case for an AppSec Program
June 26, 2025
2025-06-26 00:00:00
Learn how to frame the benefits for a C-level audience and calculate the cost savings of an AppSec program.
-
 Read nowdatasheets
Read nowdatasheetsLegit ASPM for AI-Driven Software Development
July 16, 2025
2025-07-16 00:00:00
Get details on how Legit enables and secures AI-led software development
-
January 1, 2024
2024-01-01 00:00:00
-
 Read Nowdatasheets
Read NowdatasheetsLegit MCP Server
July 16, 2025
2025-07-16 00:00:00
Find out how Legit brings ASPM to AI-led development.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: How Legit MCP Server Empowers AI-Led Development
July 17, 2025
2025-07-17 00:00:00
Learn the security implications of AI-led coding and how the Legit MCP Server is a game changer for modern development.
-
 Read Nowdatasheets
Read NowdatasheetsHow Legit Secures Vibe Coding
July 29, 2025
2025-07-29 00:00:00
Get details on how Legit secures AI-led software development.
-
January 1, 2024
2024-01-01 00:00:00
-
 Read Nowwhite papers
Read Nowwhite papersSurvey Report: Application Security Posture Management Strategies
August 20, 2025
2025-08-20 00:00:00
Get results of survey of security leaders about AppSec pains and priorities.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: AI-Generated Code and the Next Era of Secure Development
August 21, 2025
2025-08-21 00:00:00
Learn about the new reality of AI-driven software development and practical guidance for evolving your AppSec program head-on.
-
 Read Nowwhite papers
Read Nowwhite papersAppSec in the Age of AI
September 18, 2025
2025-09-18 00:00:00
Understand the new requirements for application security when AI writes code.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: AI Command Center Launch
October 8, 2025
2025-10-08 00:00:00
Discover how to gain complete visibility and control over AI-generated code, models, and MCP servers across your SDLC.
-
 Watch Nowwebinars
Watch NowwebinarsWebinar: AppSec Remediation Campaigns
October 22, 2025
2025-10-22 00:00:00
Dive into how AppSec Remediation Campaigns are transforming remediation into a measured, organized, and high-velocity practice.
-
.jpg?width=2000&height=1045&name=Blog-Image-Reality%20Check%20on%20Securing%20AI-Generated%20Code-2%20(1).jpg) Read Nowwhite papers
Read Nowwhite papersReality Check on Securing AI-Generated Code
November 5, 2025
2025-11-05 00:00:00
How are your peers thinking about AI-generated code security? We asked 117 of them to find out.
-
 Read Nowdatasheets
Read NowdatasheetsLegit VibeGuard Datasheet
November 12, 2025
2025-11-12 00:00:00
Get an overview of Legit VibeGuard capabilities.
-
 Watch Nowvideos
Watch NowvideosVideo: Introducing VibeGuard
November 12, 2025
2025-11-12 00:00:00
The Legit founders announce VibeGuard, what it does and why we built it.
-
 Watch Nowvideos
Watch NowvideosLinkedIn Live: Welcome to VibeGuard
November 12, 2025
2025-11-12 00:00:00
Watch this recording of our LinkedIn Live VibeGuard announcement and demo.
-
 Read Nowcase studies
Read Nowcase studiesLarge financial services firm remediates 90% of secrets and governs AI use with Legit ASPM
November 17, 2025
2025-11-17 00:00:00
Read how a large enterprise reined in their secrets sprawl and got eyes on AI use with Legit.
-
 Watch Nowwebinars
Watch NowwebinarsSecure AI Code from the Start - Introducing Legit VibeGuard
November 19, 2025
2025-11-19 00:00:00
Learn how AI coding assistants are transforming how software is built - and see a live demo of Legit VibeGuard.
-
 Read Nowcase studies
Read Nowcase studiesLarge financial services firm transforms its AppSec program with Legit
November 20, 2025
2025-11-20 00:00:00
Read how a large enterprise freed up resources from maintaining a homegrown ASPM.
-
 Tour Legit VibeGuardguides
Tour Legit VibeGuardguidesSelf Guided Tour through Legit VibeGuard!
November 25, 2025
2025-11-25 00:00:00
Take a self guided tour through the Legit VibeGuard platform. If you're interested in seeing more, request a demo today.
-
 Watch Nowvideos
Watch NowvideosThe Risks of AI Code Generation
November 25, 2025
2025-11-25 00:00:00
Legit co-founder Liav Caspi highlights the main security risks of AI-generated code.
-
 Watch Nowvideos
Watch NowvideosUnderstanding the Role of AI in Cybersecurity
November 25, 2025
2025-11-25 00:00:00
Legit co-founder Liav Caspi highlights the AppSec opportunities AI introduces.
-
.png?width=2000&height=1045&name=1200x627%20(1).png) Read Nowanalyst reports
Read Nowanalyst reportsAgentic Remediation: The New Control Layer for AI-Generated Code
December 9, 2025
2025-12-09 00:00:00
Read the SACR analyst overview of vibe coding and Legit VibeGuard.
-
-1.png?width=2000&name=Jan%202026%20Webinar%20(Liav%20and%20Avishag)-1.png) Watch Nowwebinars
Watch NowwebinarsSecuring AI-Generated Code: The New Blind Spot in AppSec
January 20, 2026
2026-01-20 00:00:00
Learn how security and product leaders unpack how AI-generated code changes the AppSec threat model. For security teams.
-
.png?width=2000&height=1045&name=Webinar_1%20(1).png) Watch Nowwebinars
Watch NowwebinarsAI Is Writing the Code. Who’s Responsible for What Comes Next?
January 20, 2026
2026-01-20 00:00:00
Learn how former developers turned platform and solutions leaders break down what’s happening inside modern AI-driven development workflows.
-
 Read Nowcase studies
Read Nowcase studiesLarge health insurance provider gets fast visibility into SDLC risks with Legit
February 3, 2026
2026-02-03 00:00:00
Read how the CTO and his team were struggling to get visibility into their SDLC and were introduced to the team at Legit to clearly pinpoint where security issues needed to be addressed.
-
.png?width=2000&height=1045&name=Exe_Brief_Cover%20(1).png) Read Nowsolution briefs
Read Nowsolution briefsQuestions AI is Creating That Security Can't Answer Today
February 10, 2026
2026-02-10 00:00:00
AI-assisted development is outpacing traditional AppSec governance - learn what leading security teams are doing to shore up these gaps.
-
 Read Nowwhite papers
Read Nowwhite papersThe AI Security Maturity Model for AI-First Development Teams
February 10, 2026
2026-02-10 00:00:00
Read the framework for evolving from reactive cleanup to proactive AI governance & protection.
-
.png?width=2000&height=1045&name=Guide_Cover%20(1).png) Read Nowwhite papers
Read Nowwhite papersFixing Code Issues Early to Protect Developer Flow
February 10, 2026
2026-02-10 00:00:00
Learn how AI fundamentally changes development architectures and how pre-commit governance enables velocity without friction.
-
 Read Nowanalyst reports
Read Nowanalyst reportsLatio's 2026 State of Application Security Market Report: Legit Security One-Pager
March 3, 2026
2026-03-03 00:00:00
See research analyst Latio highlight the core benefits of Legit's approach to securing code and applications. No form required.
-
 Read Nowanalyst reports
Read Nowanalyst reportsLatio's 2026 State of Application Security Market Report
March 3, 2026
2026-03-03 00:00:00
Read Latio's recently released overview of the AppSec market through the eyes of a practitioner.
-
 Watch Nowwebinars
Watch NowwebinarsHard to Handle: Securing AI-Generated Code and the AI agents That Write It
March 20, 2026
2026-03-20 00:00:00
Listen to the discussion to learn new ways to scan, test and secure both AI-coded applications and the agents that create them.
-
 Watch Nowwebinars
Watch NowwebinarsAI Writes Your Code: Who Owns What Happens Next?
March 31, 2026
2026-03-31 00:00:00
Watch the discussion with former developers turned platform and solutions leaders unpacking what's happening inside AI-driven development environments.
Request a Demo
Request a demo including the option to analyze your own software supply chain.