Application Security (AppSec) has been around for decades, but it has fallen behind application development advancements like DevOps and cloud. How did this happen and how, in a time of increasing software supply chain attacks, can AppSec quickly catch up to protect businesses for DevSecOps and scale?
AppSec has been a key pillar in establishing trust in using software for so many things – from electronically transferring money to accessing medical results online. The traditional AppSec practices of SAST, DAST, and SCA have served us well and will continue to be with us for the foreseeable future.
In simpler times, a new software release took a few months or quarters to develop and then a “code-freeze” was declared. That’s when the AppSec team came in, scanning the code for vulnerabilities and compliance issues often using SAST and SCA. This might take a couple of weeks to resolve, prioritizing the “Critical” and “High” severity security issues, followed by re-testing the entire solution including DAST. This traditional model generally worked well and was made possible with just a few AppSec engineers.
A New Era: Adoption of Agile, DevOps and Cloud
However, times change. The growing adoption of DevOps and public cloud deployment environments like AWS, Azure and GCP by the smallest startup to the largest enterprise has signaled a new era. It’s an exciting time to be a Software Engineer. New tools and methodologies that go hand in hand with a cloud-first world have become mainstream (CI/CD, microservices, serverless, APIs, to name a few). It’s hard to find an organization today that hasn’t adopted some form of cloud services and doesn’t have some sort of DevOps initiative or CI/CD pipeline for deploying software to the cloud.
This new era allows new internal and external services to be developed and changed faster than ever. And with greater flexibility to make rapid change, business leaders have benefitted from new levels of business agility, and they don’t want to go back.
How AppSec Got Left Behind
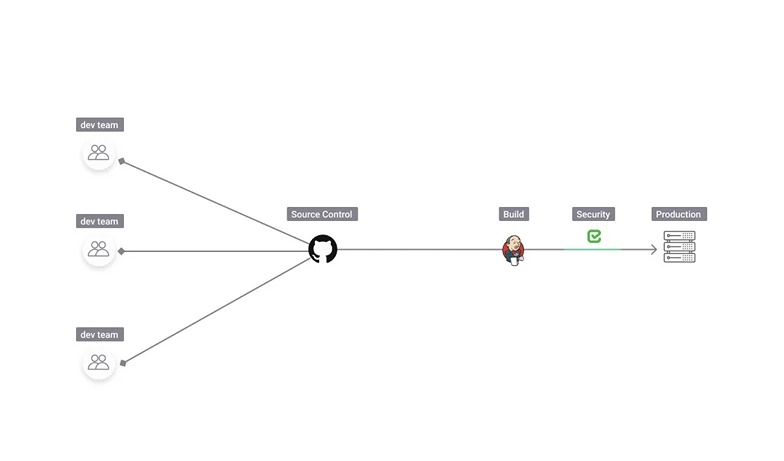
A new challenge has surfaced because of the dramatically increased speed and complexity of our new software supply chains. The software development pipelines are more complicated and automated, there’s increased reliance on 3rd parties within your SDLC, and there are more SDLC systems and infrastructure to safeguard. This has produced a larger and ever-changing attack surface beyond what AppSec has had to secure in the past. Cybercriminals have noticed this vulnerable attack surface with the rise of software supply chain attacks increasing anywhere from 3-6x per year.
It’s no secret that being part of an AppSec or DevSecOps team is challenging, in part because of the constant balancing act of remediating the most critical security issues with limited resources. But what if the traditional AppSec tools you’ve relied on are not sufficient anymore and you don’t have visibility into your most critical vulnerabilities and defects? How can you prioritize your limited resources on the most critical threats if they are hidden from view? This can be a recipe for a disaster and many security teams are in this uncomfortable position.
Blind Spots with Traditional AppSec Tools
SAST, SCA and other traditional AppSec tools are still an important part of the security picture. But what has become clear, is that they lack broader visibility and context across complex and sprawling software supply chains that needs securing.
You can think of these traditional AppSec tools like fixed position security cameras within a large bank, and the AppSec team as the security manager sitting in the security monitoring room. Each camera sees its own little area. But what if this bank has multiple entrances, a large perimeter, and lots of traffic? These fixed position cameras don’t allow you to see the bigger picture, they may not be positioned properly to see the largest threats. And if you’re short staffed you don’t have time to physically walk the bank perimeter to manually check security along the way.
Similarly, an effective AppSec program for a large, sprawling and complex software supply chain can no longer rely solely on the static placement of traditional security controls like SAST and SCA combined with manual best effort security checks. The attack surface is too large, changing too rapidly, and cyber criminals are now fully aware of typical blind spots and vulnerabilities. A new solution approach is needed to help AppSec teams regain security effectiveness and efficiency.

Must Have Features For Modern AppSec
Modern AppSec needs to holistically scan the broader software supply chain environment quickly and seamlessly. In our bank analogy, think of security cameras with the ability to scan 360 degrees and zoom in and out across the bank, supported by motion detectors that alert you to suspicious behavior in areas such as a secured vault. With better tools, the security manager sitting in the security monitoring room can be much more effective and efficient. They can obtain greater visibility, valuable context around potential risks, and do it all without requiring more staff.
Similarly in the modern application development environment, SAST, SCA and DAST tools are narrowly focused and insufficient. Today, you need to do more than scan your source code. You also need to scan your development pipelines for gaps and leaks, the SDLC infrastructure and systems within those pipelines, and the people and their security hygiene as they operate within it. New tools are required to secure the broader environment, not just the code. And modern software supply chains are constantly changing, so new solutions must have automated discovery and analysis and provide continuous assurance that software releases remain secure even as the supply chain keeps changing underneath it.
Supercharge Your AppSec, At Scale
CISOs, AppSec and DevSecOps leaders face unique challenges today. They need to secure the business from increasing software supply chain attacks, while also improving their overall AppSec effectiveness and efficiency. New security solutions that work seamlessly with existing AppSec tools and investments and can adapt and evolve right alongside a rapidly changing SDLC and CI/CD pipelines are required. Fortunately, at Legit Security we’ve developed a security platform that can address both.
If you’d like to learn more, please contact us or book a demo to see the product in action.
Download our new whitepaper.


