Use Cases
Latest Use Cases
Displaying 2 of 2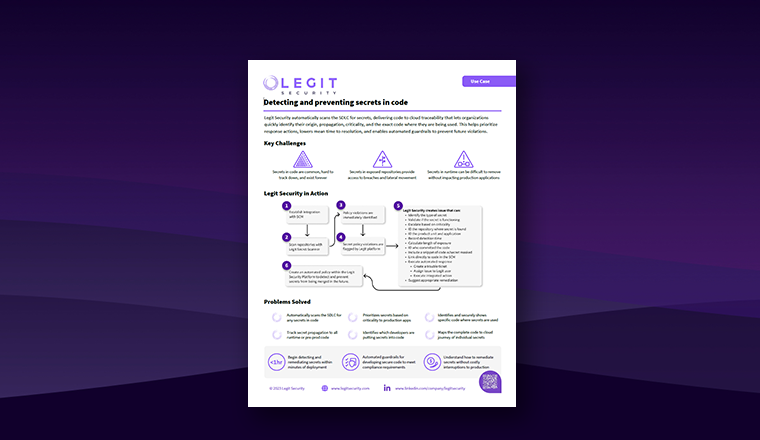
Case Studies
Detecting and preventing secrets in code
Legit Security automatically scans the SDLC for secrets, delivering code to cloud traceability that lets organizations quickly identify their origin, propagation, criticality, and the exact code where they are being used.
Read Now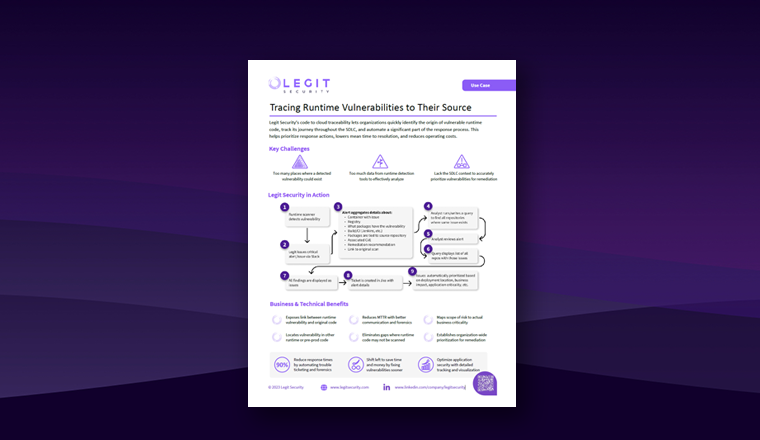
Case Studies
Vulnerabilities In Runtime
Legit Security’s code to cloud traceability lets organizations quickly identify the origin of vulnerable runtime code, track its journey throughout the SDLC, and automate a significant part of the response process.
Read NowRequest a Demo
Request a demo including the option to analyze your own software supply chain.